3 Utilities to Scan Linux for Vulnerabilities
Protecting Your Linux System from Hacker Attacks

While Linux is renowned for its robust security, it remains vulnerable to cyber-attacks. Hackers often attempt to steal valuable information or compromise the system. Therefore, it's crucial to implement additional protection measures to prevent potential issues.
In this article, I will introduce three effective, free tools to enhance your server's security. You'll learn how to scan your server for security weaknesses and malware.
These examples have been tested on an Ubuntu distribution.
Let’s dive in!
1. Lynis
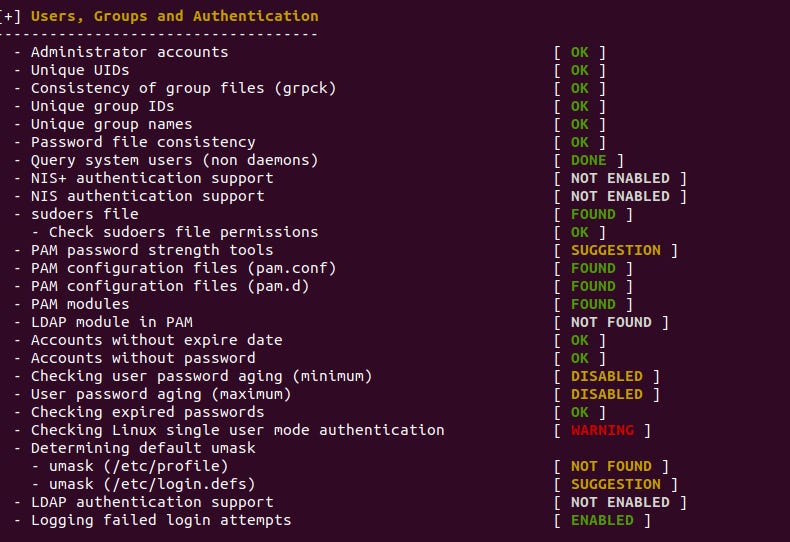
Lynis is an open-source security tool for Unix-based operating systems to detect vulnerabilities. It’s primarily used for audit and compliance testing. For example, file permissions, firewall settings, installed software, user accounts, kernel, networking, USB devices, and many more.
Installation
To install Lynis on Ubuntu, execute the following command:
$ sudo apt-get install lynisDemo
It’s straightforward to run a security check:
$ sudo lynis audit systemIt will take a couple of minutes. You should see a report with status keywords such as Found, Not Found, Disabled, Suggestion, Warning, etc.
Additionally, the tool created reports and log files containing more precise information about the scan.
/var/log/lynis.log — this log file is valuable to understand what the program did in the background. You can find recommendations for problems. For instance:
Suggestion: Set a password on GRUB bootloader to prevent altering boot configuration (e.g. boot in single user mode without password) [test:BOOT-5122] [details:-] [solution:-]/var/log/lynis-report.dat — this is a report from the audit process in a more user-friendly format.
Tip: To make your system more secure, you can schedule a cron job to run Lynis periodically and send you reports.
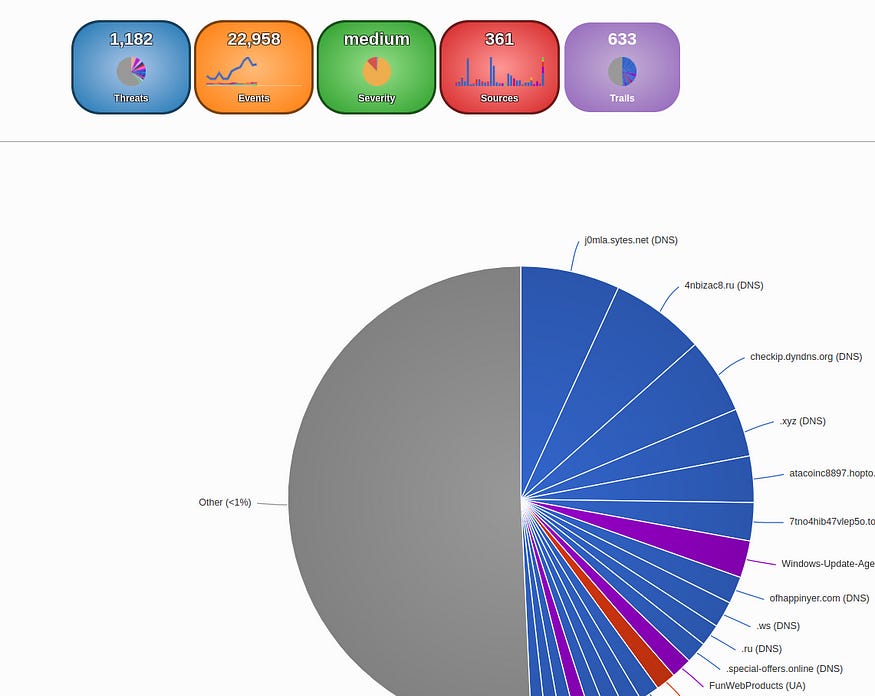
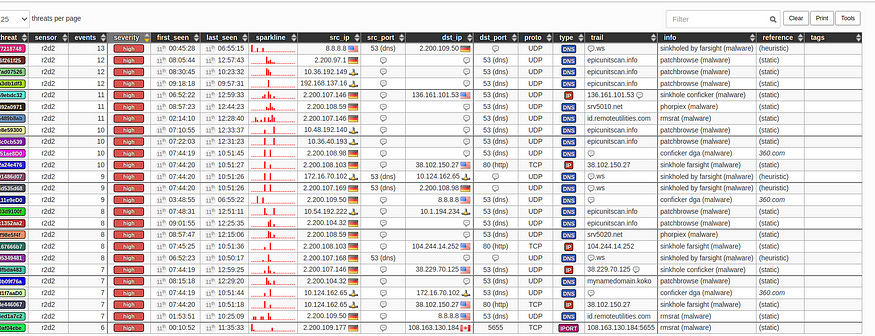
2. Maltrail
Maltrail is another useful open-source security tool. It’s mainly used for detecting suspicious traffic. It works with a database of publicly available lists of malicious and/or suspicious trails. For example, a fishy trail can be an IP address, a domain name, etc.
Installation
To install this tool on Ubuntu, run these commands to install the necessary libraries:
$ sudo apt-get install git python3 python3-dev python3-pip python-is-python3 libpcap-dev build-essential procps schedtool$ sudo pip3 install pcapy-ng$ git clone --depth 1 https://github.com/stamparm/maltrail.gitDemo
$ cd maltrail$ sudo python3 sensor.pyTo access the reporting Dashboard, open
http://127.0.0.1:8338
(login with default credentials admin:changeme!).
The Maltrail project offers a demo with real-life threats available here.
3. ClamAV
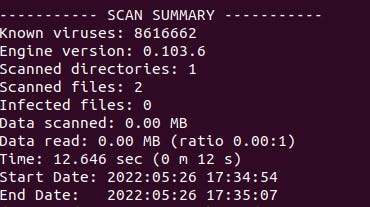
ClamAV is a free tool for detecting viruses, malware, trojans and similar threats. It’s specially designed for e-mail scanning on mail gateways.
Installation
To install this tool on Ubuntu, run:
$ sudo apt-get install clamavDemo
Once installed, you can run the freshclam service to update the list of known virus signatures:
$ sudo freshclamTo scan a directory, run this command:
$ sudo clamscan -r -i /home/user/projects/mydirIn this example, I want to scan a folder named mydir. The argument -r stands for recursive, and the -i tells ClamAV to show infected files only.
The output looks like this:
Conclusion
In this article, you learned about 3 practical tools to scan your Linux server for vulnerabilities. Depending on the use case, you can determine which one you need the most.
I hope you learned something new from this short post. Thank you for reading, and see you next time!